eDiscovery for Human Resources: A Basic How-To Guide

In today’s digital world, many businesses have gone paperless, choosing to keep important files and documents stored on computers rather than in file cabinets. Among these digitized files are, of course, the documents that HR departments prepare and maintain – e.g., company handbooks and policies, employee reviews and disciplinary actions, payroll documentation, OSHA records, and more.
Going paperless has many benefits, including search-friendliness and storage efficiency. Electronically generated and stored files also contain a huge amount of potentially useful information that is unavailable in paper form: metadata that keeps track of when, how, and by whom those files were created, modified, viewed, transmitted, and deleted.
But with these benefits come new requirements and difficulties in terms of data organization and preservation.
In the event that a possible HR-related lawsuit is on the horizon, it is often HR’s responsibility to preserve and provide all relevant company employment data in its various forms (Word documents, Excel spreadsheets, PDFs, etc.) from each of the devices where that data may live (computers, phones, flash drives, etc.). The preservation of internal email, social media posts, and other digital communications can also create large volumes of data that may be important in employee-related litigation.
This is where eDiscovery comes in.
What is eDiscovery?
eDiscovery, or electronic discovery, is the process of sifting through a large amount of data and finding any pieces that may be relevant to a specific legal action or dispute. This process is used when electronically stored information (ESI) must be provided for use in litigation, a lawsuit, or an investigation, such as the alleged unlawful firing of an employee. eDiscovery may also be used to find data related to suspected employee misconduct, such as alleged theft of company-owned trade secrets.
Some of the possible HR-related scenarios or allegations that would require eDiscovery include:
- Employee misconduct
- Employer misconduct
- Employment discrimination
- Worker safety and OSHA compliance
- Employee privacy
- Negligent hiring
- Negligent retention
- Harassment
- Retaliation
- Union relations
- Copyright infringement
- Theft of company property (physical or intellectual)
- Defamation (of an an employee or of the company)
When pending or actual litigation does arise, it is important for the HR department, as the primary caretaker of ESI, to understand how and where the data is stored. The goal is to allow the company to identify and access relevant data as quickly and efficiently as possible. This process is most effective when the HR and IT departments work together with in-house and/or outside legal counsel and an eDiscovery service.
There are several steps involved in the eDiscovery process, as shown in the Electronic Discovery Reference Model (EDRM):
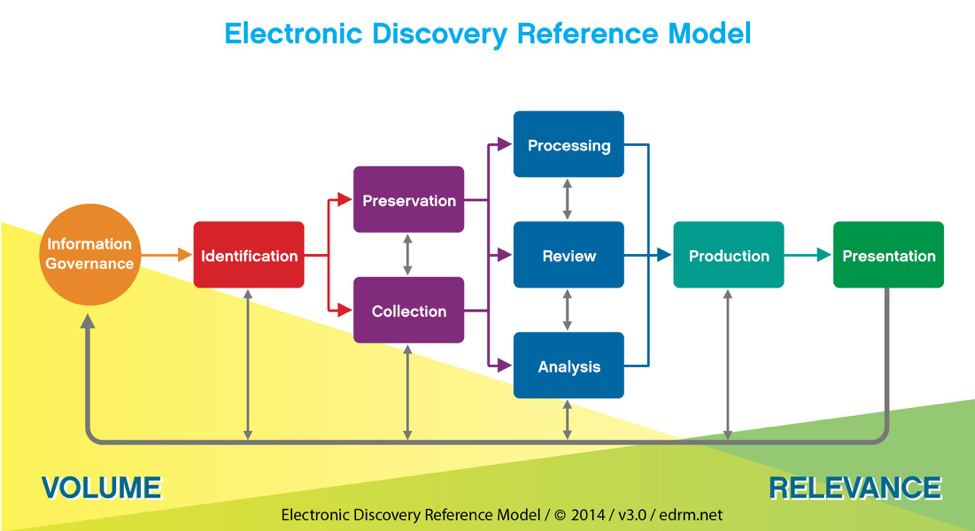
A professional eDiscovery company should be employed and consulted from the start of the eDiscovery process. The two steps in this process that HR needs to be directly involved in are Identification and Preservation.
Identification
In this step, potential sources of relevant ESI are determined.
Relevance is important because, although you want to be sure to provide all the data that will be needed to resolve a situation, providing too much data heaps on a huge amount of additional cost (as in thousands of additional dollars – maybe tens of thousands) in future steps of the eDiscovery process. These costs will come in the form of fees from the eDiscovery company you choose to employ and, much more so, lawyer fees for review of potentially relevant data.
For this reason, you may not want to identify every employee with the company as a potential source of relevant ESI. Instead, put some thought into who actually had contact with the people involved or had a hand in the situation. Often, new leads are discovered later in the process, at which time ESI can be collected from newly identified sources.
How to identify potential sources of relevant ESI:
1. Determine File Types
This may include Microsoft Office files, such as Word or Excel documents; emails; texts; social media posts; images; database files; and accounting files.
2. Interview Potential Custodians
Custodians are owners or caretakers of data, meaning they have some of the potentially relevant files on their computers, phones, thumb drives, or other devices.
Interviewing potential custodians will often lead you to identify additional potential custodians. For example, John emailed the tax files to Alice, who may have made changes.
3. Keep a Record of Your Efforts
Always keep detailed notes on every step of your process, including your interviews. Your legal council may prefer a specific format for documenting your efforts, so be sure to consult with them.
Preservation
Once you have identified potential sources of relevant ESI, you must act quickly to ensure that none of it is destroyed or altered in any way. Any changes made to or deletions of any files that are requested in a lawsuit or investigation may result in some pretty hefty court fines for spoliation (destruction) of evidence.
How to preserve potentially relevant ESI:
- Promptly send a Litigation Hold Notice, also known as a Legal Hold, in both email and written form to each identified custodian requiring them to stop using potentially relevant files. These files should not even be opened, much less modified in any way.
- Wherever possible, discontinue use of all identified devices. You may even order that these devices be collected and stored securely to ensure they will not be used.
- Ensure that backup devices used are removed from circulation so that potentially relevant ESI located on them is not overwritten or otherwise destroyed.
- Keep detailed notes of the steps you take toward preservation of potentially relevant ESI.
Types of data that may be required in a legal hold:
- Personnel records
- Applications and resumes
- Payroll documentation, including wage records, job evaluations, and merit systems
- OSHA records
- EEO-1 forms
- I-9 forms
- Employee benefits documents
- Digital conversations (emails, texts, instant messages)
eDiscovery Doesn’t Have to be Scary

Work with your IT department to put the following IG policies into place:
1. Develop an ESI Lifecycle Plan
Learn and keep track of the length of time your company is legally required to maintain specific files. Develop plans for storing ESI that must be retained and for destruction of data once its retention period has ended.
2. Use Current Storage Technology
Technology often moves forward more quickly than your files do. Be sure to always keep all data on current devices. You do not want important data to get trapped on obsolete technology, such as floppy disks.
3. Be Organized
Maintain an understandable file structure so that the correct ESI can be located quickly when needed. Make sure the organization of important data is intuitive for new users, as you may be unavailable when a situation arises in which the data is required. Also ensure that file names and folder names are clear and easy to understand. It helps to decide on a naming convention and stick to it.
Anybody tasked with searching your company’s ESI should be able to answer the following questions:
– What is this information?
– When was this file created or last modified?
– Where is this information stored?
– Who has access to this file?
– Why is this information being retained?
– How is this data being stored/protected?
4. Security
Maintain proper cybersecurity that conforms to government or industry regulations. Install appropriate firewalls, password protections, encryption, and other measures as detailed in published industry regulations and as recommended by your company IT department or chief security officer (CSO).
5. Back It Up
Maintain and regularly test effective data backup measures. It is important to note here that the court is not kind to those who have lost relevant data due to hard drive crashes and ineffective backup. In fact, this situation has been cause for spoliation fines.
6. Educate

Be Prepared
When it comes to eDiscovery, the best advice we have is to be prepared. Should something happen, you’ll need to act fast to limit liability. Control of the company’s digital environment and preservation of data before too many hands can touch it is essential.
Have an eDiscovery partner and legal council on retention before the need arises. Work with your eDiscovery partner and your company IT department to develop a plan and workflow for each variable situation. With some basic eDiscovery understanding and a plan in place, everything should go smoothly.
Note: This article does not constitute legal advice.

