Empowered Employees Are the Front Line Against Cyber Threats

For many companies, their biggest security vulnerabilities are hiding in plain sight: their employees. Willis Towers Watson claims data shows that two-thirds of cyber breaches are caused by employee negligence. Companies make significant infrastructure investments to defend against external cyber threats, yet our data shows that only 18 percent of cyber breaches are driven by external threats.
As a result of this growing recognition of the human element in cyber risk, about 75 percent of employers plan on addressing factors tied to human error in the next three years, according to the Willis Towers Watson “2017 Cyber Risk Survey”.
What will it take for employers to meet this challenge? First, they need to understand the scope of the threat. Next, they must understand the strategies that can turn their biggest security vulnerabilities – employees – into their first line of defense instead.
Assessing the Insider Threat
Most employers say they have established effective policies to manage cybersecurity threats, and most employees indicate that they understand their companies’ policies. In practice, however, employees often lack the awareness and accountability required to thwart cyber threats.
It starts with understanding. Employees often lack awareness of cybersecurity risks at a basic level. For example, a commonly held belief among employees is that their organizations’ IT systems are their ultimate protection. This thinking may explain why roughly 45 percent of employees say that it’s safe to open any email on their work computer, according to the Willis Towers Watson survey.
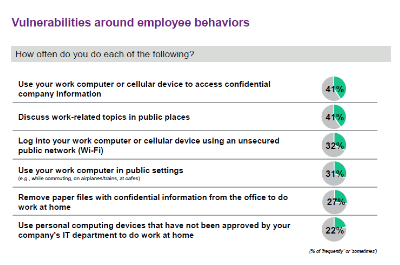
Other behaviors that threaten data privacy and security include: using a personal or public computer or cellular device to access confidential company information (approximately 40 percent); logging into a work device on an unsecured public network (approximately 30 percent); and using a work computer in public settings (approximately 30 percent).
Building a Cyber-Savvy Culture
In many respects, workforce culture drives employee behavior. This is certainly true when it comes to security Many employers indicate that they are looking to build cultures of cyber-risk awareness in their organizations to promote employee behaviors that will lessen their vulnerability to cyber threats.
Employee feedback mechanisms can enable employers to gain deeper understandings of the cultural factors influencing employees’ cyber awareness across their organization.
The following are steps organizations can take to a build strong, cyber-savvy cultures:
Encourage an Ongoing Learning Environment
As companies begin to build cyber-savvy cultures, they cannot afford to overlook or underestimate the value of tailored and specific training. In fact, our research reveals that employees in companies that experienced data breaches gave their companies significantly lower scores in the area of training compared to the ratings from employees in high-performing companies.
Moreover, based on employee responses to questions regarding how they use technology at home and at work, we defined four types of employee attitude towards cybersecurity:
- Aware: those who protect personal information in daily life and are aware of information security at work.
- Comply: those who follow data protection policies at work but are careless on a personal level.
- Ignore: those who pay attention to protecting personal information, but who don’t act with the same care at work.
- Unconcerned: those whose technology usage patterns at home and work may lead to potential cyber risks.
Our research shows that just over 30 percent of employees fall into the “aware” category, while more than 70 percent of employees exhibited safer behavior after at least a half day of training. Furthermore, employees who spend more time on cybersecurity training are more inclined to report coworkers who breach data protection policies.
Develop Cyber Talent Strategies
Employers need to cultivate robust pipelines of cyber-savvy talent. Onboarding for new information security talent should cover cyber-risk management processes and procedures. These topics should also be embedded throughout the talent life cycle, from performance management to succession planning. Likewise, an effective retention strategy for information security professionals should include ongoing training to keep their skills up to date and to enable staff to advance in their roles.
Empower Employees: Your Most Effective Defense
Robust cyber-risk management requires not only state-of-the-art technology solutions, but also effective human capital programs. It takes a culture of cyber awareness, an ongoing learning environment, and forward-looking talent strategies to build and sustain employees’ “cyber IQs.” Cyber-savvy, empowered employees will serve as your most effective defense against cyber threats.
A comprehensive cyber-risk strategy that encompasses all aspects of an organization is vital for any business in today’s threat landscape. For true bottom-up integration of cyber protections to have an impact, companies need to actively engage their employees and get them involved. It is through a strong corporate culture that organizations can create strong lines of defense and protect their valuable assets throughout the corporate hierarchy.
Suzanne McAndrew is a global business leader for the talent line of business for Willis Towers Watson.

